Uncovering the New Microsoft Password Exploit: How Windows Themes Exploit 0-Day Vulnerability
Understanding the Windows Themes Exploit
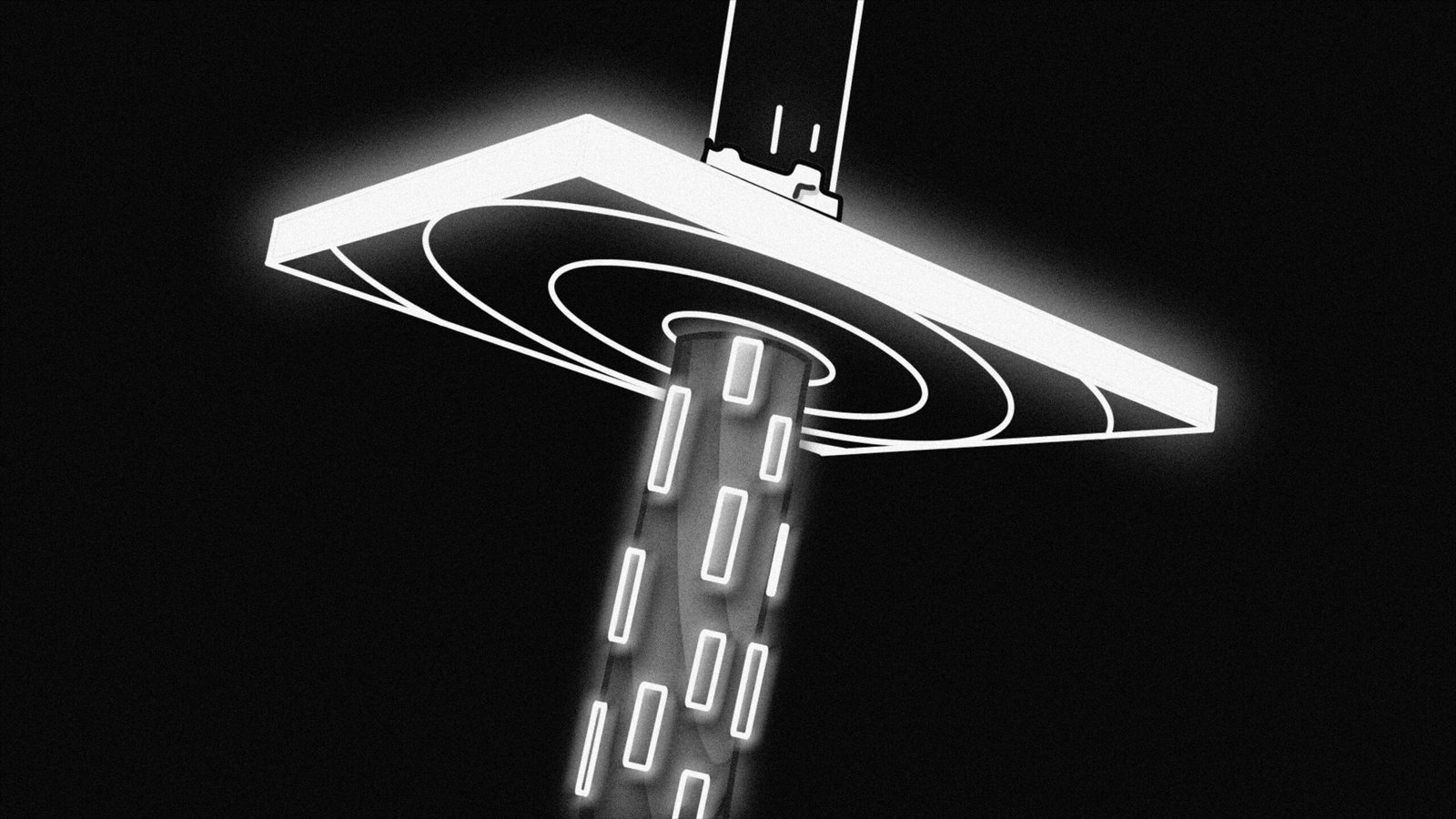
A newly discovered Windows theme and new Microsoft password Exploit exploit highlights a rather alarming 0-day vulnerability. This brings serious questions about the security of Microsoft passwords. This is a 0-day vulnerability. It’s a hole in the security of any software that the vendor has not yet discovered. A hacker can exploit it before a patch to close the hole is deployed. Here, it allows an attacker to manipulate Windows themes. This manipulation becomes the source of unauthorized access to sensitive information. This information includes user passwords.
There lies an unsuspecting user vulnerable to installing a malicious theme that executes code, breaching the system’s integrity. This type of exploitation steals login credentials. It also obtains other details by exploiting the specially prepared files placed within the package of a theme. Increasingly with time, even password cracking becomes more challenging, yet most users put passwords at greater risk. One should warn of this problem because it is easy and simplistic to apply most themes. However, nobody reads between the lines.
Risks of Unpatched Vulnerabilities: Eroding Password Security
The repercussions of the unpatched vulnerability are dire. Cybercriminals will exploit the 0-day vulnerability to access systems and passwords. This action renders password management tips ineffective. These tips are done to enhance security. Users ought to be more careful in realizing that harmless customizations can lead to serious issues in security. The very possibility of wide exploitation casts a shadow over the overall stability and reliability of Microsoft password security.
Similar vulnerabilities new Microsoft password exploit exploited in the past. These examples show the importance of consistent preventive password hack measures for users. Educational awareness about cybercriminal tactics is important. Updating software regularly could alleviate much of the risk associated with this Windows theme exploit. Comprehensive security awareness powers users to better protect their digital identities.
Real-World Implications of the Windows Security Breach
The latest Windows security breach has far-reaching implications that have brought to light the advancement of password-hacking techniques. Attackers can easily bypass standard Microsoft password security protocols by exploiting a 0-day vulnerability. This may allow them unauthorized access to user accounts and sensitive information. This can occur easily and poses a serious threat. It affects both individual users and enterprises. Therefore, it is essential to scrutinize the implications of such an exploit.
Many case studies highlight the likely consequences of such an attack. In 2022, a leading financial services company suffered a breach wherein hackers exploited a similar weakness. The attackers manipulated the password management systems. They stole the sensitive information of thousands of customers. This theft resulted in financial losses and serious reputational damage. This scenario is a powerful reminder. One cannot afford to make mistakes in password management in cybersecurity.
The Fallout of Password System Vulnerabilities: Cyber Threats and Trust Loss
The security breach also brings to light the many cyber threats that may arise from exploited weaknesses in password systems. Once hackers gain access, they may use advanced methods to escalate privileges within the system, thus compromising entire networks. The consequences go beyond immediate financial losses. Organizations often face legal battles. They must also make unrelenting efforts to regain client trust.
Therefore, organizations need to take the initiative to prevent password hacking from occurring. That should not be merely having a policy on passwords but rather investing in continuous security education for its staff. Such moves will help secure against these evolving techniques the cyber hackers use. Since this attack landscape continues to shift, users should be prepared. They must be responsive to emerging threats associated with vulnerability like in this case.
Preventing Password Hacks: Essential Management Tips
The importance of safeguarding sensitive information is crucial. We must keep new exploits like 0-day vulnerabilities locked up and under wraps. This should continue until a cure or a means to handle this has surfaced. People must enhance their password management practices regarding attacks targeting Windows themes from the software giant, Microsoft. This applies at both personal and organizational levels as hackers exploit techniques like password cracking.
First, good passwords are a must. Good passwords should be at least 12 characters long. They must include both uppercase and lowercase letters. The inclusion of numbers and special characters is also important. Avoid common words and birthdays. Even password managers can help you generate more complex passwords and store them safely. This saves time from remembering numerous passwords but enhances security as a whole.
Password Security: The Importance of Regular Updates and Multi-Factor Authentication
Updating your passwords is something that should not be understated. Passwords should be changed at least every three to six months to minimize unauthorized access. This is very critical during or after a security breach has been identified. Alternatively, if you’re working on a device that was unsafe in the past, change passwords. Implement multi-factor authentication for additional security. MFA makes the system require two or more verification factors. These factors could be some knowledge of the user, such as a password. They could also include something that the user has, like a mobile device. This reduces the possibility of unauthorized entry very significantly.

Additionally, updating the software and the new Microsoft password exploit will prevent password hacks. Most updates of software have patches for known vulnerabilities that hackers could exploit. It is important to check and install updates on all applications, operating systems, and security software regularly. This prevents exploitation of the same vulnerabilities, especially newly discovered ones, such as the recent 0-day vulnerability.
By implementing these effective tips on password management, a person can significantly reduce the risk of password compromise. This action greatly improves overall cybersecurity efforts.
Conclusion: Final Thoughts on Cybersecurity and Password Protection
A 0-day Windows theme vulnerability has led to the emerging new Microsoft password exploit. This situation calls for a high necessity for solid cybersecurity. Knowledge of such vulnerabilities is crucial for individuals. It is also essential for organizations in today’s rapidly shifting digital world. Password hacks have intensified to alarming proportions. Therefore, it becomes pertinent to introduce tips and best practices. These will help handle password management to minimize associated risks from hacks.
Key Insights on Password Security: Prevention, Complexity, and Proactive Cybersecurity
Important issues about password security were revealed throughout the entirety of this paper. They were well-established to reflect on the cracking of current passwords. Preventive action must be taken to guard against hacking. This includes using complex passwords, implementing multi-authentication factors, and maintaining updates in the security protocol appropriately. In the present times, it can also be stated that networks should have proactive cybersecurity against network exploits.
To show the damage that might happen due to poor password security, think about a small business company. This company doesn’t maintain any uniform practice regarding passwords. One compromised password can create a domino effect. This would expose the company to unauthorized access to sensitive customer information. It would also lead to crippling financial losses. Additionally, there would be an irremediable loss to the company’s goodwill. So, in this example, vulnerabilities exist. They need to be identified. Appropriate security measures must be taken after identifying them.
There is a need for a joint effort toward protection. Reflection on these major themes highlights this necessity. A culture of awareness and proactive cybersecurity actions can make a difference in defense exploitation. To have readers take it seriously, further resources and tools would help bolster password security. By prioritizing such initiatives, one may increase overall security against emerging threats.